Your screenshot won't survive a legal challenge. Here's what will
Chain of custody isn't just for courts. When a reader asks "how do I know you saw this?" — here's what journalists and newsrooms need to know about web archiving and chain of custody.
Why screenshots won't hold up — and what journalists should use instead
A colleague sent me a screenshot last month. A public figure had posted something ugly, she grabbed it in time, and the post was gone within the hour. She had her record – or so she thought.
The question of what that record is actually worth — to her editor, to a subject who threatens legal action, to a reader who asks "how do I know?" — is one I've been working on for a long time. Not primarily as a legal question, though it is that too. As a journalism question. A question about the conditions under which you can stand behind what you publish.
The problem with screenshots
Screenshots are everywhere in modern reporting. They're fast, they're familiar, and they feel sufficient: you saw it, you grabbed it, you have it – right? The problem is that feeling is not a record.
A screenshot is a photograph of your screen at a moment in time. It contains little metadata that can be independently verified. It cannot prove when it was taken, whether the page it shows was real, or whether the image has been altered since. Anyone with a phone and a photo editing app can produce one that looks identical to yours. German courts have said this explicitly, but the vulnerability isn't really a legal technicality.
When the subject of your story says the screenshot is fabricated, you have no technical answer. When your editor asks what you can actually prove, "I took this screenshot" is not the foundation you want to be standing on.
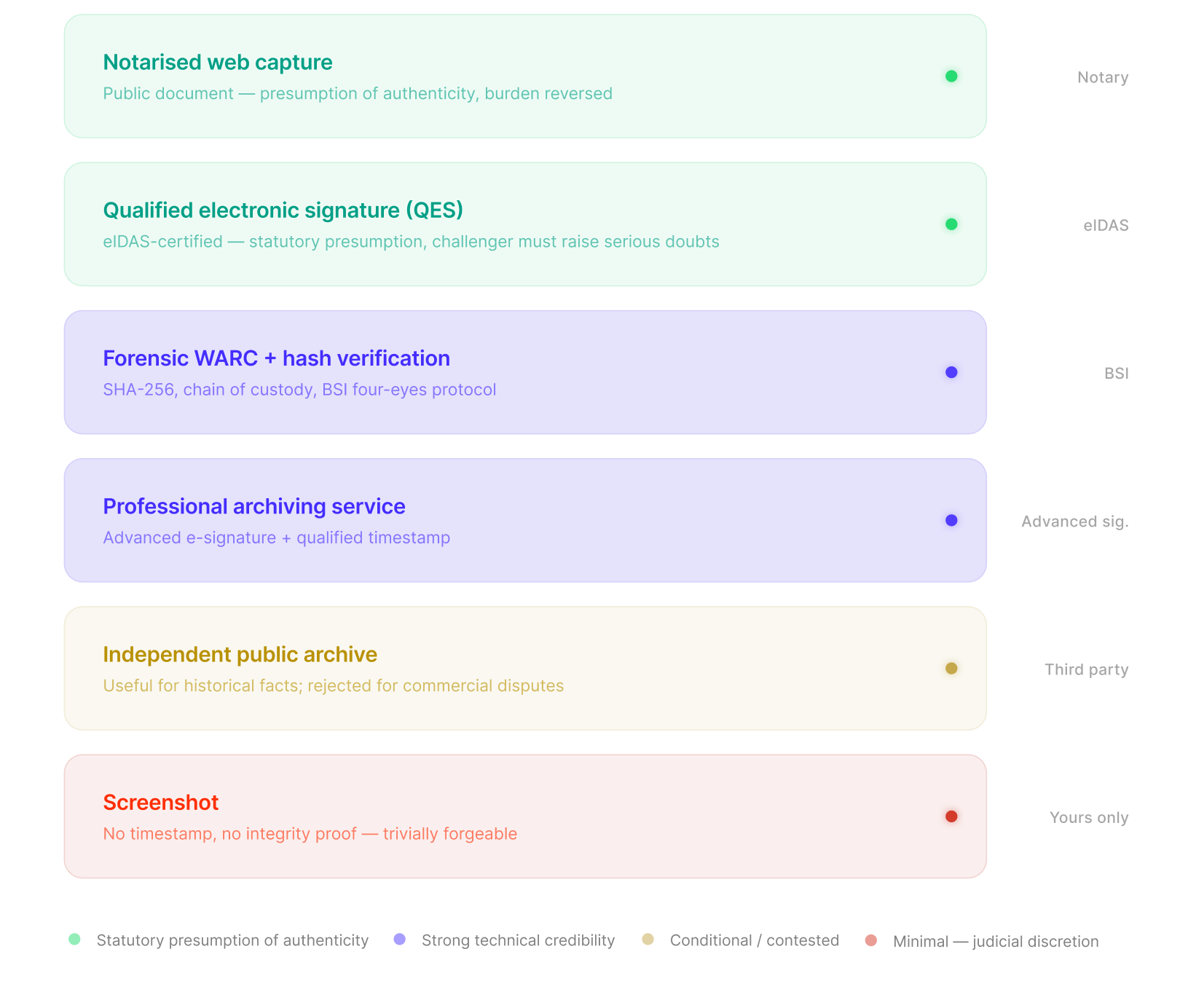
What a real record looks like
I've spent years on this question — at Airwars, through the Digital Evidence Toolkit, now at the Starling Lab. The problem keeps appearing in the same shape: reporters and investigators who collected material diligently, in good faith, using whatever was at hand, and then found that material challenged precisely when it mattered most.
What makes the difference, in my experience, is whether the capture is witnessed. Not by a person, necessarily, but by a process that is independent of you and cannot be altered after the fact.
This means: a full archive of the page — its content, its assets, its structure — stored in a format that preserves everything. A cryptographic fingerprint of that archive, generated at the moment of capture, so that anyone can verify nothing has changed. A timestamp from a certified service, so the when is established by something other than your say-so.
The format that does all of this is a WARC — a web archive, the same format used by national libraries and the Internet Archive. Not a JPEG. Not a PDF. A WARC captures what was there: the page's full text, images, the DOM structure, HTTP headers.
Where a screenshot is but a memory, a signed WARC is a witness statement.
For readers, too
There's a dimension of this that isn't about legal protection at all. It's about transparency with readers — about what we owe people who read what we publish.
When I embed an archived capture in a story and it comes with a cryptographic timestamp and a chain of custody log, I'm not doing that for a judge. I'm doing it because a reader has the right to ask "how do I know you saw this?" and I want to have an honest answer. In an environment where the question "is this real?" is asked about everything, showing your work is part of the job.
The provenance of your sources is part of the story. Not in an academic, footnote-heavy way — but as a basic act of accountability journalism. I captured this. Here is when. Here is the fingerprint that proves it hasn't changed.
What the infrastructure looks like
None of this requires exotic tooling anymore. The pieces exist.
A browser extension that captures a full WARC of the page you're looking at, including content behind logins and paywalls. Cryptographic signing via C2PA — the same standard now being built into cameras by Sony and Nikon, and adopted by AFP, the BBC, and others. A certified timestamp tied to the capture. All of it stored somewhere your newsroom controls, searchable, replayable.
This is what evidx is built to do — and why we've been building it for newsrooms rather than as a general consumer product. The threat model is specific: you're preserving sources for stories that may be challenged, by subjects who are motivated and resourced. The tool needs to match that reality.y.